Vulnerability Management Tools play a significant role in detecting, analyzing, and patching vulnerabilities in web and network-based applications. The most common words used in security speak of vulnerability, risk, and threat.
Risk is the potential for damage or loss, and threat is an adverse event that exploits a vulnerability. Finding these weaknesses is crucial to protecting every asset and the company’s data. A vulnerability is a weakness or loophole in a system that can threaten it.
The vulnerability management tools aim to identify problems. Many security researchers and companies use the Common Vulnerability Scoring System (CVSS) to rank vulnerabilities by severity.
Tools regularly scan the system or network for vulnerabilities and obsolete software to safeguard it from outside and internal threats. It encompasses the processes, plans, and tools for finding, assessing, and reporting system or network security vulnerabilities.
Before starting the vulnerability management process, specific tasks must be completed, such as determining the scope, selecting tools to identify vulnerabilities, providing the team’s roles and responsibilities, and creating policies and SLAs.
Four Essential Steps In The Vulnerability Management Procedure
- Identifying Vulnerabilities: – Various vulnerability scanners are used to scan the system, devices working in a network, databases, virtual machines, servers for open ports, and services to identify potential security flaws.
- Evaluating Vulnerabilities: – Identified vulnerabilities are then evaluated using the risk score the organization operates, and these vulnerabilities are focused on accordingly.
- Treating Vulnerabilities: Three approaches, Remediation, mitigation, and acceptance, are used to treat vulnerabilities based on their priority.
- Reporting Vulnerabilities: Reporting is essential to any assessment or process. Vulnerabilities found need to be appropriately documented, including steps to reproduce, impact, and mitigation.
Enhancing infrastructure security with vulnerability management solutions makes it more efficient for users and harder for attackers to access. These tools can uncover vulnerabilities and fix them before an attacker does.
Here Are Our Picks For The 10 Best Vulnerability Management Tools In 2024 And Their Feature
- Intruder: Automated vulnerability scanner with proactive monitoring and cloud-based security insights.
- Qualys: Comprehensive cloud-based platform for continuous vulnerability management and compliance.
- Acunetix: Specialized in web vulnerability scanning with accurate detection and reporting.
- Tripwire: Provides robust security configuration management and file integrity monitoring.
- Astra Pentest: Offers continuous vulnerability assessments with detailed reports and actionable remediation guidance.
- Rapid7: Integrated platform for vulnerability management, detection, and response.
- Syxsense: Combines endpoint management with real-time vulnerability detection and patching.
- F-Secure: Delivers proactive vulnerability scanning and threat intelligence for enhanced security.
- OutPost24: Scalable network security assessment with continuous monitoring capabilities.
- BreachLock: Cloud-native platform for AI-powered vulnerability scanning and pentesting services.
Best Vulnerability Management Software – 2024 Features
| Vulnerability Management Tools | Keywords | Stand Alone Feature | Pricing | Free Trial / Demo |
|---|---|---|---|---|
| 1. Intruder | 1. Proactive scanning for emerging threats 2. Attack surface monitoring and reduction 3. Streamlined cloud security with AWS, GCP, and Azure integrations 4. Asset discovery and network scans 5. Actionable remediation advice and compliance reporting |
Automated network vulnerability scanning. | Starts at $99 per month | Yes |
| 2. Qualys | 1. Vulnerability management 2. Asset discovery and inventory 3. Vulnerability assessment 4. Patch management integration |
Cloud-based continuous security monitoring. | Pricing varies. Contact for a quote | Yes |
| 3. Acunetix | 1. Web vulnerability scanning 2. Deep scanning capabilities 3. OWASP Top 10 coverage 4. Network scanning |
Comprehensive web application security testing. | Pricing varies, contact for a quote | Yes |
| 4. Tripwire | 1. Configuration Management 2. Vulnerability Management 3. File Integrity Monitoring (FIM) 4. Security Configuration Assessment |
File integrity monitoring and compliance. | Contact for custom pricing | No |
| 5. Astra Pentest | 1. Automated Scanning 2. Deep Scanning Capabilities 3. Intelligent Fuzzing 4. Customizable Testing Profiles |
Managed pentesting with actionable reports. | Starts at $699 per scan | Yes |
| 6. Rapid 7 | 1. Vulnerability Management 2. Penetration Testing 3. Incident Detection and Response 4. Application Security |
Dynamic application security testing. | Starts at $5,775 per month | Yes |
| 7. Syxsense | 1. Endpoint Management 2. Patch Management 3. Security Assessment and Monitoring 4. Remote Control and Troubleshooting |
Unified endpoint vulnerability management. | Starts at $600 per year | Yes |
| 8. F-Secure | 1. Endpoint Protection 2. Threat Intelligence 3. Incident Response and Forensics 4. Vulnerability Management |
Advanced threat detection and response. | Pricing based on solutions needed | No |
| 9. OutPost24 | 1. Vulnerability Management 2. Web Application Security 3. Network Security 4. Cloud Security |
Scalable vulnerability management and assessment. | Contact for pricing details | Yes |
| 10. BreachLock | 1. Vulnerability Assessment 2. Penetration Testing 3. Web Application Testing 4. Network Security Testing |
Penetration testing as a service (PTaaS). | Custom pricing is available upon request. | Yes |
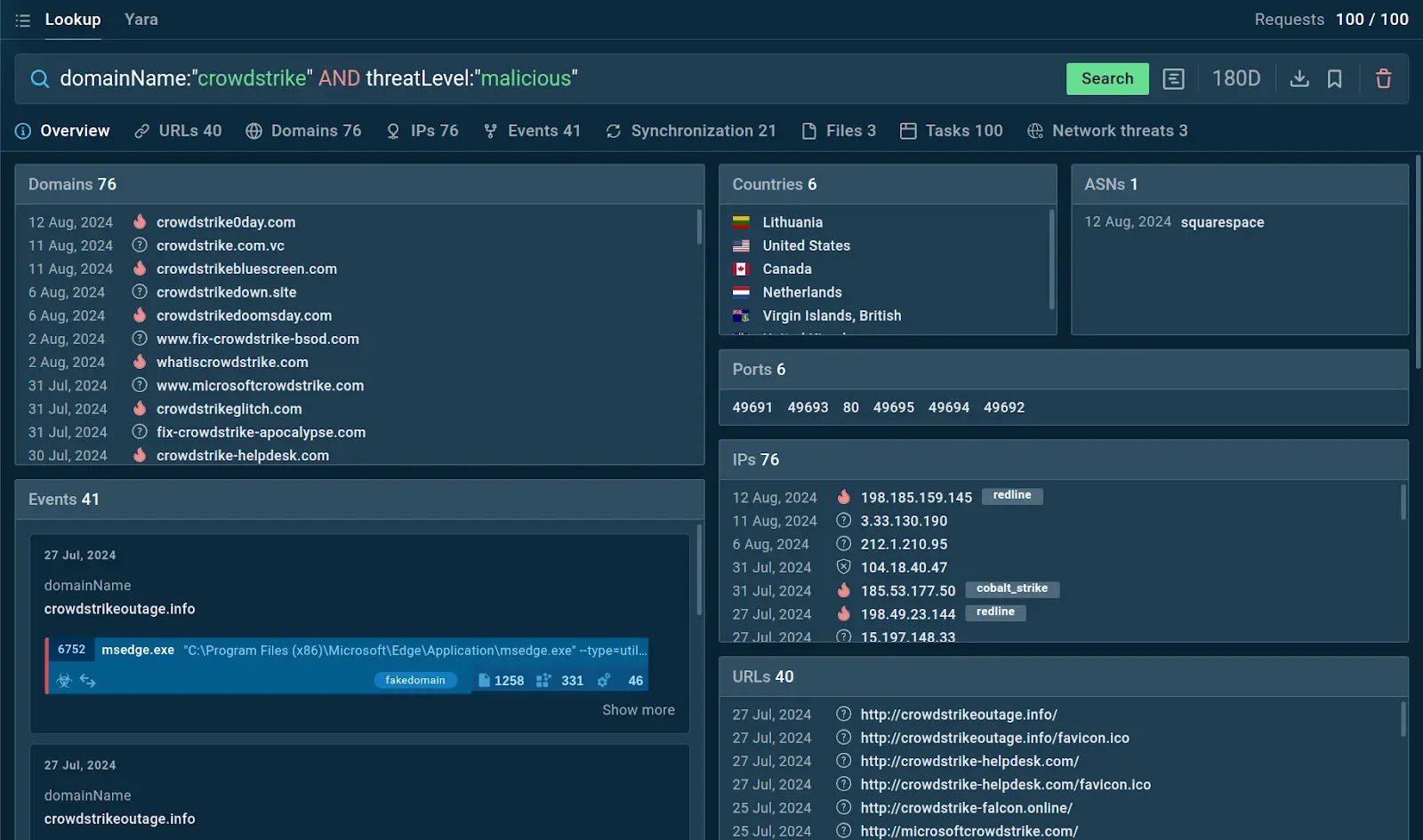
1. Intruder
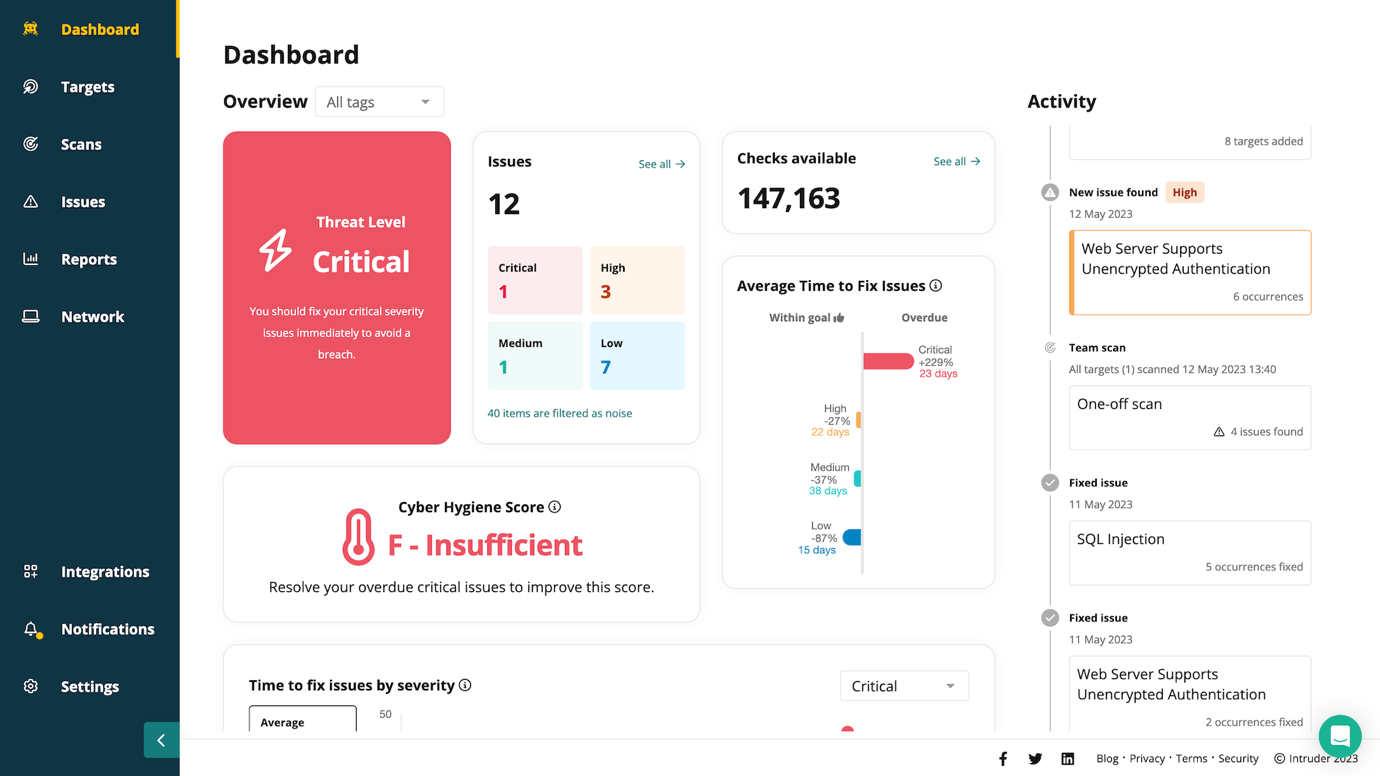
Intruder combines continuous network monitoring, automated vulnerability scanning, and proactive threat response in a single platform. This approach provides a detailed view of your attack surface so you can fix the most critical weaknesses quickly and effectively.
Intruder reports can show partners and clients your security commitment or comply with ISO 27001 and SOC 2. In addition, Intruder’s Cyber Hygiene Score tracks how long it takes to remedy issues and how you compare to industry standards.
You can easily integrate Intruder with your cloud providers (AWS, Azure, Google Cloud), get proactive alerts when exposed ports and services change across your digital estate, and automatically scan your systems when anything changes.
Features
- Proactive scanning for emerging threats
- Attack surface monitoring and reduction
- Streamlined cloud security with AWS, GCP, and Azure integrations
- Asset discovery and network scans
- Actionable remediation advice and compliance reporting
| What is Good? | What Could Be Better? |
|---|---|
| Thorough checks and scans that run proactively | Bolt-on options like bug hunting are only available on the Premium and Vanguard plans. |
| Expert team of penetration testers | Improved integration with more tools. |
| Straightforward to use and intuitive design | Enhanced user interface design. |
| Multiple developer integrations with tools such as Jira, Slack, GitHub, and more | Faster scanning and reporting times. |
| Excellent and responsive support team | |
| Shows assets that are exposed to the internet | |
| Compliance automation & high-quality reports |
2. Qualys
Qualys, a vulnerability management tool, identifies all environmental assets and assesses risk across vulnerabilities, support, and asset categories for proactive risk mitigation. It lets firms easily catalog software, hardware, and unmanaged network assets and mark key assets.
This tool is compatible with patch management solutions and configuration management databases (CMDBs), allowing for fast vulnerability discovery, prioritization, and automated, scalable remediation of vulnerabilities to reduce risk.
All of the discovered hardware, including databases, servers, and networking components, is automatically classified by Qualys. It also records the software, services, and traffic installed on the system, along with their current running states.
Features
- With Qualys’ vulnerability management tools, you can find and rank vulnerabilities in networks, systems, and apps.
- With Qualys, businesses can find and list all of their IT assets.
- It has tools for continuous monitoring that let you always see how secure your IT assets are.
- It helps businesses make sure they are following security rules and industry laws.
- Finds security holes in old systems automatically.
- Check and understand danger across all of your networks automatically.
- Assessment of the security of a multi-cloud system.
| What is Good? | What Could Be Better? |
|---|---|
| Quickly remediate threats at the scale. | Most of the features require licensing. |
| Manage asset vulnerabilities throughout the complete vulnerability lifecycle. | It takes a long time to fetch the scan results. |
| Ecstatic user interface and information accuracy. | Poor customer support. |
| There are little to no false positives due to cloud agents. | The mobile endpoint is not as well defined as the cloud endpoint. |
3. Acunetix
Acunetix is a powerful vulnerability management software specializing in web application security, offering automated scanning to detect and remediate a wide range of vulnerabilities, including SQL injection, XSS, and other web-based threats.
The software provides detailed vulnerability reports and integrates seamlessly with popular development and CI/CD tools, allowing organizations to identify and address security flaws early in the development cycle, enhancing overall security posture.
Acunetix supports both on-premises and cloud deployments, offering flexibility and scalability for businesses of all sizes, while its intuitive interface and comprehensive dashboard make vulnerability management efficient and straightforward.
Features
- Websites and web apps that Acunetix checks for security holes are scanned automatically by the company.
- Acunetix uses advanced testing methods to find vulnerabilities more thoroughly.
- Acunetix finds vulnerabilities in web applications listed in the OWASP Top 10 and the CWE/SANS Top 25.
- These lists are widely used as industry standards for web application security.
- Finding network-based vulnerabilities and devices tied to the network is possible with Acunetix’s network scanning tools.
- Acunetix instantly adds a vulnerability to its list and marks it as “Open.”
- Testing again to make sure the flaws were fixed correctly.
- It makes macros that can automatically scan places protected by a password.
| What is Good? | What Could Be Better? |
|---|---|
| Scans multiple domains in very little time. | Some versions of the tool are not stable. |
| Detect over 7,000 vulnerabilities, including zero-days | Fewer configuration options for scans. |
| Able to schedule daily, weekly, and monthly scans. | Pre-recorded login sequence specifications are more challenging. |
| Initially, it’s easy to set up and configure. | Does not support multiple endpoints. |
4. Tripwire
Tripwire Vulnerability Management Software provides continuous monitoring and assessment of your IT environment, identifying vulnerabilities across servers, networks, and cloud infrastructures, enabling organizations to prioritize and remediate risks effectively.
The software integrates with existing security tools to deliver actionable insights, helping security teams focus on high-risk vulnerabilities and ensure compliance with industry regulations and internal security policies.
Tripwire’s solution offers automated patch management and configuration control, reducing the attack surface while maintaining system integrity, making it a critical component of a comprehensive cybersecurity strategy.
| What is Good? | What Could Be Better? |
|---|---|
| What is Good? | Unimpressive technical support. |
| Advanced vulnerability scoring method. | Creates unwanted network traffic. |
| Lower network impact. | Inconsistencies in some of the vulnerability findings. |
| Audience-specific reporting. | Not great with vulnerability tracking. |
5. Astra Pentest

Astra Pentest, in addition to manual pen testing, is a sophisticated automated vulnerability management application that assesses and displays asset vulnerabilities.
In addition to over three thousand automated and manual pentests, the platform checks assets for critical vulnerability issues (CVEs) listed in the OWASP top ten and SANS 25. It includes every test necessary to comply with GDPR, HIPAA, and ISO 27001 standards.
Admins can easily track and control vulnerabilities using the no-code dashboard. The CVSS score, prospective losses, and total corporate effect determine vulnerability risk scores. ISO 27001, SOC 2, PCI-DSS, HIPAA, and GDPR exams are available.
| What is Good? | What Could Be Better? |
|---|---|
| Integration with CI/CD platforms, Slack, and Jira. | It has fewer integration options available. |
| Maximizes the return on investment (ROI). | It may not be capable of detecting some malware attacks that slip through. |
| Accurate risk scoring and thorough remediation guidelines. | Astra requires external dependency, i.e., manual pentesting. |
| The support is excellent, quick, and thorough. |
6. Rapid 7
Rapid 7 InsightVM and Nexpose, an on-premise vulnerability scanner, handle vulnerabilities. By combining multiple security technologies, Rapid 7 lets the team automate procedures, monitor the network, manage vulnerabilities, analyze and stop threats, and more.
Nexpose helps you reduce threat exposure by prioritizing risk across configurations, controls, vulnerabilities, and real-time change assessment. As far as pen-testing applications go, Rapid 7 is your best bet.
Nexpose simplifies asset grouping by remediation responsibility and makes it easy to generate remediation reports for asset teams—Integrated Reconnaissance, Payload, and Closure capabilities in a single program.
| What is Good? | What Could Be Better? |
|---|---|
| Track and communicate the progress. | Frequent updates and console lockups. |
| Easy implementation of RESTful API. | Scheduling can become a nightmare if not monitored closely. |
| Integration with over 40 technologies. | Scan with Credentials can not be customized or prioritized. |
| Advanced remediation, tracking, and reporting capabilities. | The agent covers fewer compliance issues. |
| Extensive collection of templates for scanning the asset. | The tool does not have a real-time threat protection module. |
7. Syxsense

Syxsense is a top vulnerability management solution because it can see and understand every endpoint in the cloud, on-premises, and any other place or network. It uses artificial intelligence and industry expertise to monitor and protect endpoints, preventing and neutralizing threats.
Syxsense secures via managed services, 24/7 coverage, and compliance. Patch management and vulnerability scanning help firms align cybersecurity with IT management.
Syxsense makes remote computer connections without acceptance easy. This helps non-technical folks. Syxsense’s dynamic searches prioritize device groups and fixes to fit company needs. System configurations, severity, risk, and affected operations may change these traits.
| What is Good? | What Could Be Better? |
|---|---|
| Zero Trust features are integrated into Syxsense. | Over slower connections, remote control tools can be a little “flakey.” |
| Easy to connect to a user’s machine remotely. | Switching between monitors is not so good. |
| No need to manually upload updates. | Often runs into duplicate device IDs for end-user machines. |
| Ease in packaging the software. | The gap in assessing and deploying patches. |
8. F-Secure
F-Secure, renamed Secure, is a powerful and easy-to-use vulnerability management tool. It is an all-in-one vulnerability assessment and management platform providing clear, actionable, and prioritized visibility into threats to support organizations’ security strategies.
Protect yourself from modern attacks and ransomware with this cloud-based software. It incorporates automatic patch management, continuous behavioral analytics, vulnerability management, and dynamic threat intelligence.
The application may check for vulnerabilities throughout the day and inform users. The F-Secure Elements Vulnerability Management API employs JSON and HTTP methods, including GET, PUT, POST, and DELETE.
| What is Good? | What Could Be Better? |
|---|---|
| Real-time protection. | There is no protection from zero days or forensics. |
| It scales as the system grows with time. | Lack of ready-to-use templates for compliance checks. |
| Automated and customized reports. | Occasionally blocks too many executables, thus making the system slow. |
| Scan templates give an easy way to store a set of options. | Some false vulnerability issues exist in the results. |
| Less resource utilization with background protection. | Occasionally blocks too many executables, thus making the system slow. |
9. OutPost24
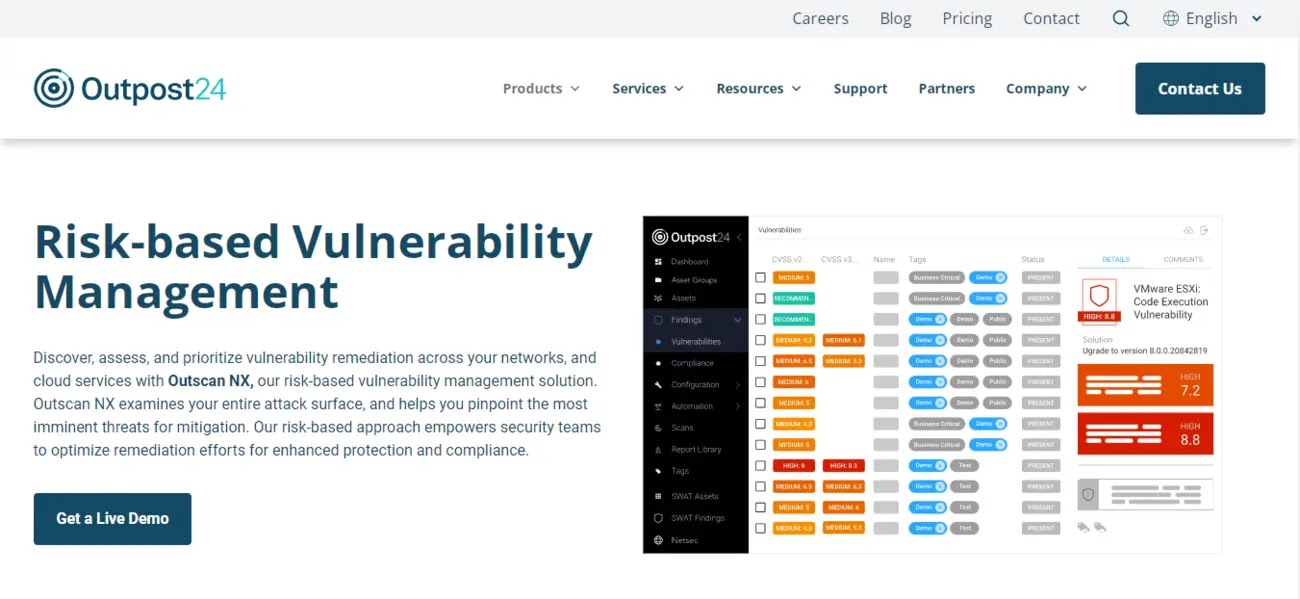
OutPost24 offers a unified vulnerability management platform that provides continuous monitoring, detection, and remediation of security risks across networks, applications, and cloud environments, ensuring comprehensive protection against potential threats.
The software delivers real-time insights into vulnerabilities, allowing security teams to prioritize and address high-risk issues efficiently, reducing the likelihood of breaches and improving overall security posture.
OutPost24 integrates seamlessly with existing security tools, enabling automated workflows and streamlined processes that enhance operational efficiency and help organizations maintain compliance with industry regulations and standards.
| What is Good? | What Could Be Better? |
|---|---|
| Ensures compliance and easy reporting. | GUI, dashboards, and reporting are the major drawbacks. |
| User-friendly internal vulnerability scanner. | It isn’t very easy and requires extra effort to maintain. |
| Improves prioritization and focused remediation. | Reports contain numerous false positives. |
| Risk-based vulnerability management solution. |
10. BreachLock
BreachLock offers a cloud-based vulnerability management solution that combines automated scanning with manual penetration testing, providing comprehensive insights into security gaps and delivering actionable remediation steps to enhance an organization’s security posture.
The software integrates seamlessly with existing workflows and tools, offering continuous monitoring and real-time reporting, which enables security teams to quickly identify, prioritize, and mitigate vulnerabilities across their IT infrastructure.
BreachLock emphasizes ease of use and scalability, making it suitable for organizations of all sizes. At the same time, its AI-driven platform ensures accurate detection of vulnerabilities with minimal false positives, improving overall efficiency.
| What is Good? | What Could Be Better? |
|---|---|
| Fast, scalable, and effective. | Needs to enhance the support |
| Extensive collection of learning material. | Hidden fees for using different features. |
| Integration with Jira and the reporting capability. | The product needs to become more resilient. |
| Extensive collection of learning material. | Security thresholds need to be increased. |
| Managed service offering. | |
| Compliance management |
The post 10 Best Vulnerability Management Tools In 2024 appeared first on Cyber Security News.